As more distributed generation comes online, as more customers opt into load-management programs, as utilities expand substation and grid automation, are we making the grid less secure? Not necessarily, says Steve Chasko, a Landis+Gyr solution director and security expert.
Chasko admits that distributed energy resources (DER) do open a few new attack vectors, but they also make the grid more secure by adding resiliency. To keep vulnerabilities in check, Chasko sees three areas requiring vigilance. “Be concerned about the anonymity of transactions, the integrity of the messaging and the integrity of the system itself,” he says.
Risk and reward
What concerns people about DER and security is the control factor. One classic attack vector Chasko points to is a load-shedding switch. “Let’s say the goal of the attack is to get it in an undesired state. If it’s on, turn it off; if it’s off, turn it on,” he explains. Either way, a coordinated attack on several switches might impact circuit loading and voltage. But the value of such technology – which helps utilities reduce peaks, defer distribution-system investments and offer customers money-saving rates – makes it worth securing.
 Likewise, distributed generation has some added risk. “DER have benefits in terms of resiliency, but if inverters on solar panels were to be compromised in such a way that some unauthorized source started shutting off power feeding the grid, that’s an attack vector that didn’t exist before. An attack could create consequences that are not desired in terms of backflow of power onto the grid or surges and spikes in demand,” Chasko says.
Likewise, distributed generation has some added risk. “DER have benefits in terms of resiliency, but if inverters on solar panels were to be compromised in such a way that some unauthorized source started shutting off power feeding the grid, that’s an attack vector that didn’t exist before. An attack could create consequences that are not desired in terms of backflow of power onto the grid or surges and spikes in demand,” Chasko says.
Distribution automation is a similar security trade-off. “If something happens to the grid, automation allows you to detect the problem more quickly and, in many cases, fix it quickly, as well,” he notes. “That gives you security advantages, so even though automation presents some new attack vectors, automation comes with positives, too.”
Under wraps
Still, Chasko says, security begins with time-tested and familiar approaches. For example, privacy of customer data has always been a utility target. When it comes to maintaining anonymity of transactions, that now covers knowledge of what’s happening with distributed energy resources (DER).
“When equipment runs … for instance, when a thermostat is set to cool the house in summer… it indicates when someone is or isn’t home,” he notes. The same is true for pool pumps and other often-controlled loads. It’s true for rooftop PV generation, too. “If the sun’s out and a generator is not able to provide power back to the grid, that tells you whether somebody’s home or not.”
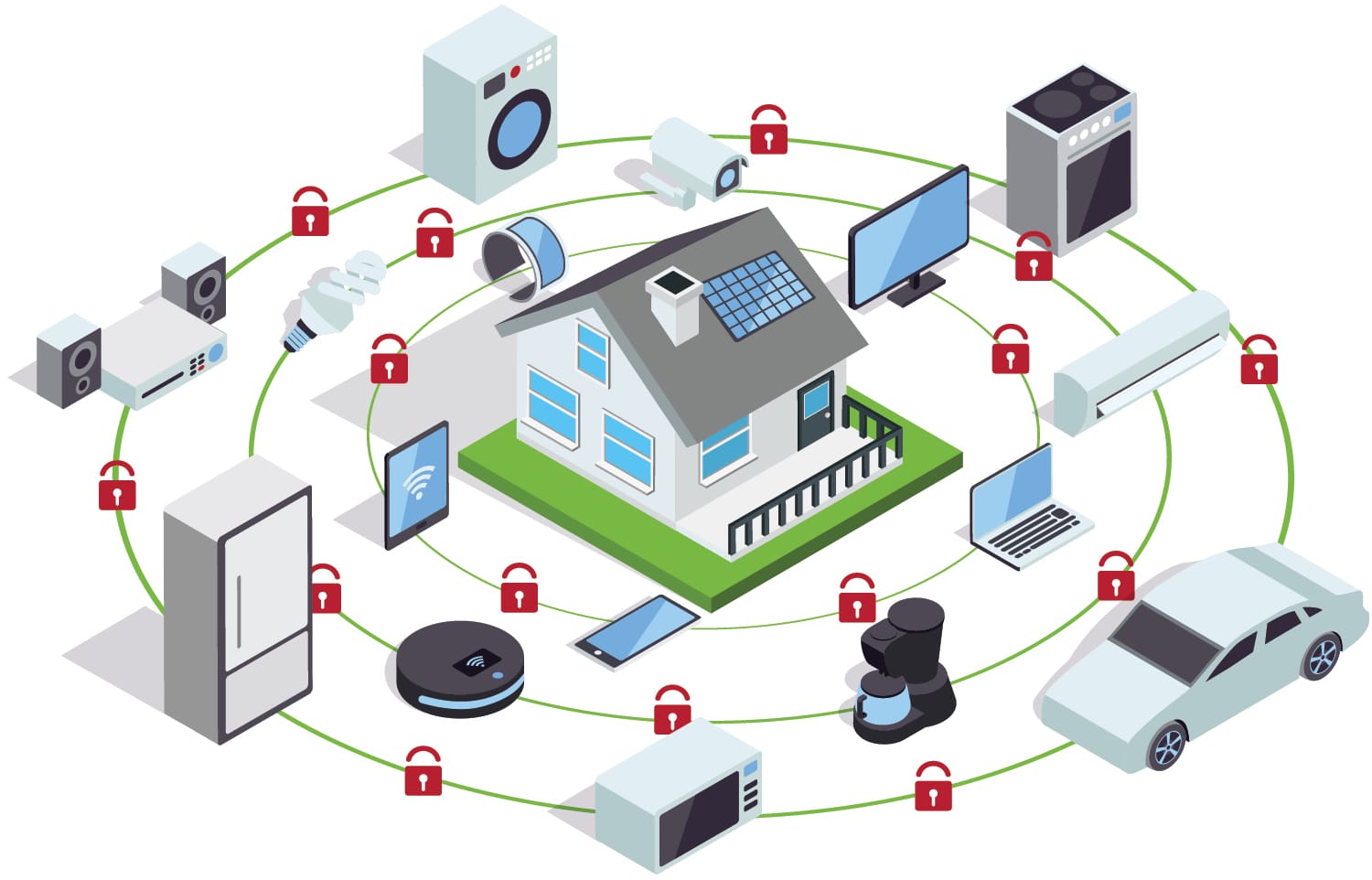
As for maintaining the integrity of messaging, Chasko notes that message authentication codes and signatures are the most common data protection approaches, and he advises utilities to have “end-to-end, application-layer cryptography from endpoints and devices near the endpoint.” The cryptography should be maintained all the way through the network in such a way that even intermediary devices between endpoints and head-end systems don’t share the same encryption key as the two devices that are communicating. In other words, the applications between an endpoint and a head-end should communicate as if they are in a private network. Think of this as a virtual private network for applications.
“Some communications solutions have intermediary devices that see unencrypted data for a mass quantity of devices, making those rich attack targets,” Chasko explains. “By having end-to-end encryption, you don’t have that. If you did have something in the middle that served as a decrypt/encrypt device, you’d want to make sure that data was properly protected.”
All around
As far as system-level protections, Chasko notes that these involve securing the individual components of the system and having controls in place to ensure devices are properly locked down. “Unused ports are closed, test ports are shut off, the device is manufactured properly, the proper level of software is running at both the head-end and endpoint … and only approved parties can update that software,” he says.
When there are upgrades to software, install them, he adds. One large data breach in recent years occurred after a company failed to install software updates that closed the vulnerabilities hackers leveraged.
Not only do utilities need to protect customer data, so do their partners. Although the breach in question didn’t necessarily result from DER, this past summer The Wall Street Journal reported that a large, west coast investor-owned utility paid federal fines to the North American Electric Reliability Corp. after a third-party contractor improperly copied utility data and then left it exposed online in a non-password-protected site.
According to NERC, this left “sensitive information” vulnerable for more than two months. In a notice to the Federal Energy Regulatory Commission, NERC explained that the data breach exposed “30,000 asset records, including records associated with Critical Cyber Assets (CCAs). The records included information such as IP addresses and server host names.”
 Usernames and passwords associated with the exposed databases also remained online and unprotected. “Exposure of the username and cryptographic information could aid a malicious attacker in using this information to decode passwords,” NERC noted.
Usernames and passwords associated with the exposed databases also remained online and unprotected. “Exposure of the username and cryptographic information could aid a malicious attacker in using this information to decode passwords,” NERC noted.
NERC also maintained, “These violations posed a serious or substantial risk to the reliability of the bulk power system (BPS). The CCAs associated with the data exposure include servers that store user data, systems that control access within [the utility’s] control centers and substations, and a supervisory control and data acquisition (SCADA) system that stores critical CCA Information.”
The utility wound up paying some $2.7 million for two violations of NERC Critical Infrastructure Protection (CIP) reliability standards.
This event looms as an important lesson now that many utilities are using load aggregators to implement fast-ramping demand response and virtual power plant applications. Ahead, NERC CIP standards will likely evolve along with the technologies and market.
Already, “New CIP standards apply to control centers that control an aggregation of DERs of at least 1500 MW in a single interconnection,” noted Stewart Ramsay is a senior partner with Vanry and Associates, in a recent T&D World article. He adds: “I believe this is a clear indication that FERC and NERC recognize that protecting generation, including DERs, plays a role in grid security.”